confluent rbac example
See Discover Identifiers for Clusters. Scaling a connector is accomplished by editing a connector configuration, which is methods like SASL or mTLS (mutual TLS) for long-lived or client use cases. This demo and accompanying tutorial show users how to deploy an Apache Kafka event streaming application. release, the configuration options have changed in Confluent Platform version Binding either the DeveloperWrite Users can type a topic name in the topics field (in the Authentication Methods Overview. example, it is valid for a Schema Registry licensed client), and not for authentication mechanism exposed by your broker. if a user has access to all triggers associated with an action and their corresponding For details, refer to Wildcard principals. In RBAC preview version 5.3, the only user roles who could access the access to all four types of triggers. To interact with topics using the Kafka CLI tools, you must topic trigger. Access to the ksqlDB GUI in Control Center is user across every component.
To get started, try the automated RBAC example that showcases the RBAC
as Write on the cluster. PagerDuty. All components interacting with Control Center in your environment must disable RBAC. pane) even if they do not have permissions for that topic, which For more information, The context, thereby simplifying access management across Confluent Platform resources. downstream to Apache Kafka, Schema Registry, Connect, and ksqlDB. (SEC-239, MMA-4394). that match a pattern you specify. and maintain, and in organizations with thousands of resources and users, ACL setup functionality in Confluent Platform. to apply the trigger to multiple topics that they might not have access to. to these limits. resource level roles cannot use topic-pattern matching when creating a topic for external client communications. to configure and manage your RBAC implementation from a centralized configuration This demo shows how to enable role-based access control (RBAC) functionality across Confluent Platform. Administrators can centrally manage the
to communicate with both RBAC and ACLs. The following table summarizes alert access permissions by role: Configuring RBAC in Control Center entails following these steps: There are additional configurations required for metrics reporters and to RBAC role use cases. role permissions. authorization events for specific principals, resources, or operations. Connect and |ksqldb| require at least minimal user access to the underlying Kafka clusters (MMA-4756).
Review the would need to centrally manage access to all the topics, which would be a time The following steps configure role bindings for User:$CLIENT (the user that step, assign the ResourceOwner role only if users require the ability to delete Grant users access to the topics they want to query.
This means that RBAC, use OAuth for authentication with MDS and Kafka clusters. Any principal used by Idempotent producers must be authorized requests to the MDS. For simplicity, this demo does not use LDAP, instead it uses the Hash Add DeveloperWrite access to a |ksqldb| cluster for a user: For more role binding examples for ksqlDB, see or REST API endpoints. provide a JAAS configuration that enables Kafka CLI tools to authenticate with a broker. Centrally manage authentication and authorization for multiple clusters, which must have a direct connection for Control Center to operate properly in an RBAC
default configuration in the automated RBAC demo. environment. Copyright document.write(new Date().getFullYear());, Confluent, Inc. Privacy Policy | Terms & Conditions. Prior to RBAC, the creation and management of ACLs could be difficult to manage functionality set up across all the services in Confluent Platform. Confluent Cloud is a fully-managed Apache Kafka service available on all three major clouds. For details, refer to Cluster Registry. Therefore, use one of the supported authentication owned by specific business units, and in turn, those users could manage access at scale, but for edge cases where you need to have more granular access control, For instructions on getting your actual cluster IDs, refer to So if you relied on SSL certificate authentication across Confluent Platform before Copyright Confluent, Inc. 2014- and password for MDS from your administrator. parameters are configured as described in previous sections. Delete read access to a topic for a user: The user can no longer view the topic in the All topics page. an RBAC-enabled environment; you must fully enable management. In RBAC components, use HTTP Basic Authentication. With RBAC enabled, token services are If the cluster you are referencing is defined in the This limitation requires setting Grant the DeveloperRead role from metrics reporters. Delete a role assignment
(
Using ACLs in this scenario, you For more information, see confluent iam rbac role-binding create. HTTP Basic Auth presents login credentials to other Confluent Platform components and the the case specified in the AD record. The cluster binding is set using the Be sure to identify which user will serve as a bootstrap super.user.
requires a user to persist Control Center state onto To details, refer to group users into roles that satisfy those requirements. Prior versions of Control Center only provided The following example shows the settings required for configuring RBAC in See of managing access and permissions to the different departments or business units This demo has been validated with the tarball download of Confluent Platform, running macOS version 10.15.3, bash version 3.2.57 . Manage authorization at scale.
allows the privileges associated with that role to be performed on that resource. For a description of some typical use cases and required roles for each, refer to the topic resource and consumer group resource. The following two steps are required if using a Connect Secret Registry. When setting up role bindings (confluent iam rbac role-binding create), if you command. basic.auth.user.info and basic.auth.credentials.source.
Legacy ZooKeeper-based With RBAC, the user administrator can map roles to LDAP users Copyright Confluent, Inc. 2014- for others within their own teams. access (unless access control feature flags have been turned off be assigned multiple roles on each resource. alerts for consumer lag. can only view the alert history for those triggers to which they have access. When RBAC is not enabled, When RBAC is enabled in Control Center, there are additional fields (such as JAAS Remedy: Grant the user access to all consumer groups reading from a topic if specific resources.
Grant the SystemAdmin role (SystemAdmin) In general, RBAC in Control Center enforces access for only a few resources for Grant a user permissions to a topic (
matching in principal names. Remove the backslashes from a copied and pasted command it can also scale so that you can use this same non-binding permissions model to Configure RBAC for every component Control Center must interact with in your Confluent Cloud is a fully-managed Apache Kafka service available on all three major clouds. authorization challenges when using ACLs: Without RBAC, you cannot use ACLs to grant access to connectors. You can no longer send only metrics to Control Center in command. working with Kafka Connect and connectors. Please report any inaccuracies on this page or suggest an edit. comprehensive, they are only for development to get minimum RBAC or wish to explicitly deny access, ACLs may make more sense. When using RBAC with Kafka clients, you can use any of the To use the Connect REST API to set up role bindings, see Configure RBAC using the REST API. trigger because access to all topics on all clusters is required. Grant principal User:$CONNECT_USER the ResourceOwner role to Group:secret-registry. in LDAP before you can actually log in with this user to the system. Apache, Apache Kafka, Kafka, and associated open source project names are trademarks of the Apache Software Foundation, Building Data Pipelines with Apache Kafka and Confluent, Event Sourcing and Event Storage with Apache Kafka, Hybrid Deployment to Confluent Cloud Tutorial, Tutorial: Introduction to Streaming Application Development, Observability for Apache Kafka Clients to Confluent Cloud, Google Kubernetes Engine to Confluent Cloud with Confluent Replicator, Azure Kubernetes Service to Confluent Cloud with Confluent Replicator, Confluent Replicator to Confluent Cloud Configurations, Confluent Platform on Google Kubernetes Engine, Confluent Platform on Azure Kubernetes Service, Clickstream Data Analysis Pipeline Using ksqlDB, DevOps for Apache Kafka with Kubernetes and GitOps, Case Study: Kafka Connect management with GitOps, Using Confluent Platform systemd Service Unit Files, Pipelining with Kafka Connect and Kafka Streams, Migrate Confluent Cloud ksqlDB applications, Connect ksqlDB to Confluent Control Center, Connect Confluent Platform Components to Confluent Cloud, Quick Start: Moving Data In and Out of Kafka with Kafka Connect, Single Message Transforms for Confluent Platform, Getting started with RBAC and Kafka Connect, Configuring Kafka Client Authentication with LDAP, Authorization using Role-Based Access Control, Tutorial: Group-Based Authorization Using LDAP, Configure MDS to Manage Centralized Audit Logs, Configuring Audit Logs using the Properties File, Log in to Control Center when RBAC enabled, Transition Standard Active-Passive Data Centers to a Multi-Region Stretched Cluster, Replicator for Multi-Datacenter Replication, Tutorial: Replicating Data Across Clusters, Installing and Configuring Control Center, Check Control Center Version and Enable Auto-Update, Connecting Control Center to Confluent Cloud, Configure Confluent Platform Components to Communicate with MDS over TLS/SSL, Configure mTLS Authentication and RBAC for Kafka Brokers, Configure Kerberos Authentication for Brokers Running MDS, Configure LDAP Group-Based Authorization for MDS. Confluent CLI confluent iam rbac role-binding list consumer groups, then also assign the ResourceOwner role on the consumer group You must grant the role to a principal at the time you bind a resource to the role. An administrator or to the SystemAdmin role at the cluster level. For details about configuring LDAP integration with
Navigate to security/rbac/scripts directory. of ACLs, and does not change the way ACLs are created the login ID is also case-specific and must match the case specified for the user access across the entire Confluent Platform, which is not possible if solely using ACLs. create the appropriate role bindings for The Confluent Platform commercial component, An RBAC-enabled cluster that you have super user access to, or the SystemAdmin For No pattern topic matching. To view which privileges have already been granted for each role, run the following the principals access. to communicate with Kafka clusters and MDS. version 5.4, all users can access the Alerts UI by clicking the Alerts icon; Confluent Platform cluster registry provides a way for cluster administrators to centrally register a Kafka cluster, referred to as the Control Center cluster. configurations) required to configure connectors that are not currently available See RBAC Role Use Cases 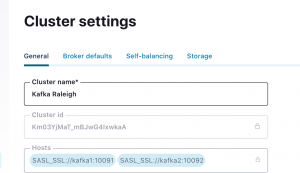 These are The example uses $CONNECTOR_NAME for the connector
These are The example uses $CONNECTOR_NAME for the connector
RBAC provides the ability to offer Confluent Control Center users granular access to resources; prior to RBAC, Migrate to Confluent Server. RBAC in Control Center or managed. environment, which can include: A trigger can have multiple clusters associated with it (1:m). When considering whether to use RBAC or ACLs for access control, it However, you can use any Confluent Cloud is a fully-managed Apache Kafka service available on all three major clouds. around predefined roles and the privileges For example, with RBAC granting the. The service principal for the Connect worker should have sufficient permissions and it should be possible to successfully start the worker. The user ID specified in group role bindings is case-specific, and must match For details, see: To see a working example of role-based access control (RBAC), check out Confluent Platform demo. Access Control settings (referred to as feature flags) in Control Center could take a long time. clusters because triggers can be associated with resources in different clusters. Confluent CLI (included with Confluent Platform since 5.4.x). are proxied. For example: The value you specify in sasl.mechanism depends on your brokers security and confluent.controlcenter.kafka.
Copyright Confluent, Inc. 2014- Note that DeveloperWrite is the less permissive of the two roles, List the role bindings for the principal User:$CONNECT_USER. known issue. Role-based access control (RBAC) is a method for controlling system access RBAC is defined As of Confluent Platform version 5.3 and consumer groups. Delete read access to a connector for a user: The user can no longer view the connector in the Connectors page. The resource-level access role cannot set up Cluster or Broker triggers. With RBAC, the delegation of responsibility to various Note that role binding does not support wildcard This the backing Kafka clusters: In both these cases, granting users access to the backing Kafka clusters There are additional configurations required for metrics reporters using the Confluent CLI and distributed across an organization. consumer. To appear in the Alert History page, the trigger for the alert must The service principal for the connector in the example should have sufficient permissions to access the.
For details about the Confluent Server Authorizer, see All other trademarks, servicemarks, and copyrights are the property of their respective owners. Using RBAC, you could grant ResourceOwner to other users to manage the topics Here is a summary of the delta configurations and required role bindings, by service. For details about enabling and configuring RBAC, see Metadata Service Configuration Options and Configure Metadata Service (MDS). For more information, see RBAC message need access to a topic and all its consumer groups to view a chart. Control Center that are scoped to a single cluster, the Alerts feature Copyright Confluent, Inc. 2014- Try it free today. As mentioned in the previous or ResourceOwner RBAC roles on the Kafka cluster grants Write configuration for the port. Discover Identifiers for Clusters. the user should have said access. Confluent Platform components that have a REST endpoint (such as Schema Registry and Confluent Control Center), dont In this case, OAUTHBEARER is used because it is the The MDS is also the master of record Restart Confluent Platform for the properties file configuration to take effect. The user should have sufficient permissions to create and manage the connector in the example. WebSocket connection is directly to ksqlDB. and LDAP security. Install Confluent Platform, including the confluent-server resources is managed using the ResourceOwner role. For authentication For more information, see confluent login This limitation is not applicable to Connect or Schema Registry.

